How to Apply the 7 Risk Management Framework (RMF) Process Steps

Art Clomera, Vice President, Operations We’ve all heard the adage: “Nothing ventured, nothing gained.” In essence, you have to risk something if you want to get things done. So much of our lives involves assessing risk and intelligently managing those risks to meet our needs and achieve our goals. It’s why a motorcyclist wears a […]
Clarifying SSDF: An Overview of the Secure Software Development Framework

Art Clomera Vice President, Operations In response to President Biden’s Executive Order on “Improving the Nation’s Cybersecurity (14028)“, the National Institute of Standards and Technology (NIST) designed the Secure Software Development Framework (SSDF). The creation of the SSDF was a strategic move to bolster the cybersecurity posture of Federal agencies. NIST also developed the Risk […]
Building ROMs for Cybersecurity Needs: A Guide for Federal Agencies

R. Shawn Elliott President and LLC Manager IPKeys Technologies, LLC | Chickasaw Nation Industries (CNI) Cybersecurity budgeting is rarely straightforward, since threats evolve faster than procurement cycles. That’s why Rough Order of Magnitude (ROM) estimates are so valuable. Whether you’re managing FedRAMP authorizations or preparing for next year’s funding cycle, a solid ROM gives you […]
Demystifying POAM: Definition, Template & Example Walkthrough

Art Clomera, CTO, Federal Services – Wouldn’t perfection be great? Everyone, every organization, every system working exactly the way they should with inexhaustible, flawless precision from the word “Go.” Never worrying about something not going exactly as planned. It sounds pretty great but also pretty impossible… (even boring). Perfection in the world of cyber security […]
NIST 800-53: What is it and What are the Control Families?

Art Clomera, Vice President, Operations Ensuring the security of information systems is a complex but necessary task that virtually every modern organization must undertake to some degree or another. One effective method of tackling information system security is to use the Risk Management Framework (RMF) developed by the National Institute of Standard and Technology (NIST). […]
What is OSCAL in Cybersecurity? (And Why it Matters)
Art Clomera, Vice President, Operations Developing software to support any federal agency’s mission is a multi-faceted task today. Cyber threats, development complexity, and meeting operational mission requirements including security boundary continuous monitoring, is growing in complexity and resources. Additionally, achieving or maintaining an authorization to operation (ATO) remains a resource intensive task, burdened by very […]
Is Zero Trust the Answer to the Federal Government’s Cybersecurity Woes?

Shawn Elliott, President, Federal Solutions We all know that cybersecurity is a top priority for all federal agencies. In Executive Order (EO) 14028, Improving the Nation’s Cybersecurity, the President initiated a sweeping government wide effort to ensure that baseline security practices are in place. A key component of this EO was to “develop a plan […]
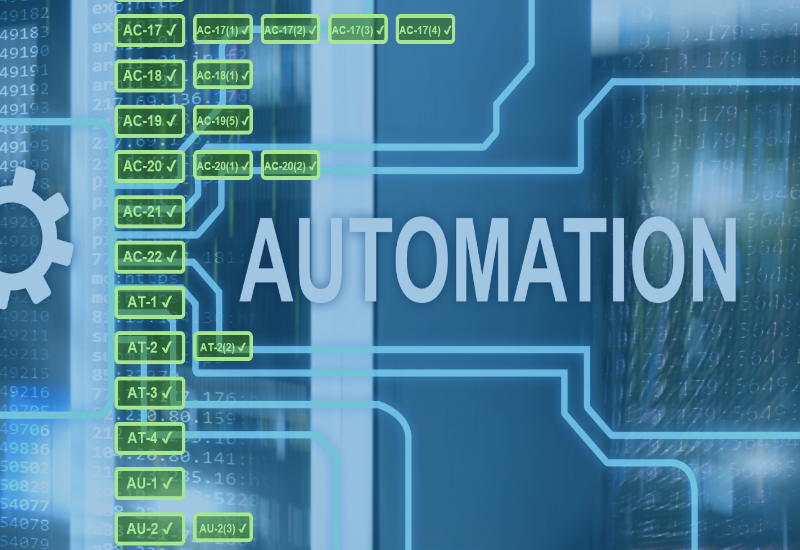
Cybersecurity Automation: How to Strengthen Defense While Reducing Manual Work

Art Clomera Vice President, Operations India, the US, Indonesia, and China alone account for almost half of the total reported cyberattacks in the government sector. Threats, ranging from espionage to malware designed to disrupt critical national infrastructure, are a defining feature of modern geopolitical relations. This barrage demands always-on, predictive, continuously improving advanced cybersecurity measures. […]
Proactive IT Risk Management: Building Resilience in an Evolving Digital World

R. Shawn Elliott President and LLC Manager IPKeys Technologies, LLC | Chickasaw Nation Industries (CNI) 2024 brought some harsh cybersecurity lessons for everyone working in U.S. government cybersecurity. One major wake-up call came when Chinese hackers broke into several U.S. telecom networks in an attack dubbed Salt Typhoon. Then came an unexpected hit. CrowdStrike, which […]
NIST Security Controls Explained (with Examples)

Art Clomera Vice President, Operations Federal agencies would be paralyzed without the data centers and software systems that store and process data. But many cyberattacks aren’t politically motivated. Government agencies worldwide are often targeted for the vast quantities of personal information they keep about citizens. The market for this stolen data is more lucrative than […]